This article is intended to discuss the nature of developing technology in-house versus utilizing third parties and some associated key hazards to tech entrepreneurs and investors.
“Mercenaries and auxiliaries are useless and dangerous; and if one holds his state based on these arms, he will stand neither firm nor safe… The fact is, they have no other attraction or reason for keeping the field than a trifle of stipend, which is not sufficient to make them willing to die for you.”
The Prince, Chapter XII - Niccolo Machiavelli
Historical Allegory
In a mountain pass just northwest of modern day Beijing in 1211, Jin Dynasty forces were preparing to hold out against a swiftly moving Mongolian army led by Genghis Khan. By this point in his life, Khan had unified the vast Mongolian tribes into a single empire that was spreading its borders with legendary brutality and unfaltering discipline. Wanyan Yongji, the Jin Emperor, however, was confident the Mongolians were no match for his forces. He had gone so far as to build a roughly 200 mile long wall, referred to as the “Jin Dynasty Great Wall”, and was paying the Ongud, a Mongol tribe, a handsome amount to secure its northern border.
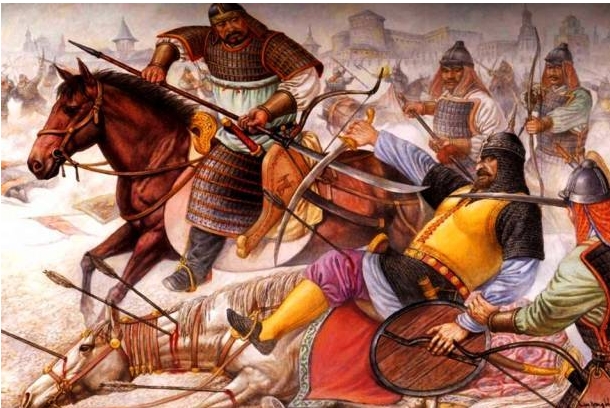
As the Mongolians advanced south, hugging the Great Wall, the previously immense Jin forces seemed to instantaneously shrink as the outnumbered Mongolian forces increased in numbers. Those that remained pledging allegiance to the Jin Emperor were confused as to what was proceeding, and then were swiftly murdered, staining the ground adjacent to the Great Wall dark red with their blood. After breaking through these defenses, the Mongolians rested one month and moved on to the capital city after rapidly winning two more battles on their journey south.
This leads one to question what happened at the Great Wall that would render it so useless against attack, why the Jin forces apparently dwindled as the Mongolian forces swelled, and how the Mongolians had stockpiled enough resources to immediately confront the Jin army after this first victory. Let’s look at some background leading up to these events. As the threat of the nearby Mongolian Empire reached the central city, Emperor Yongji decided to build a wall that would slow down any potential invasion and provide the Jin an advantage in resources and position. To help guard the Wall, he paid the Ongud tribe an immense amount to gain their loyalty. For about 10 years, he would regularly reimburse the Ongud, who were all too eager to collect their money, and smugly reveled in the peace that his work had seemingly provided his Empire.
Unknown to him, the Mongolians had been fostering relations with the Ongud and several other mercenary groups. Because of their good standing politically among one another, the Mongolian Empire had been stockpiling resources near the Great Wall for several years in preparation for battle. The Jin mercenaries were not concerned with these actions of the Mongolians as long their hefty collection from the Emperor was not threatened.
Once Genghis Khan decided to strike, the mercenaries, who had heard great stories of his army’s power, immediately defected to his side and helped slaughter the Jin soldiers at the Great Wall. The magnitude of the victory was compounded by another mercenary messenger sent by the Jin, who defected as well, and revealed all of their positions. Their swift descent into the Jin imperial city was then facilitated by the years of stockpiled resources the Ongud had allowed them to amass.
The ending of this story should add further weight to this lesson. Because of the immense amount of supplies they still had remaining, the Mongolians and their acquired mercenary army were able to siege the imperial city residents. Within the city walls, Emperor Hushahu, who had acted upon the newly-formed disenfranchised attitude within the empire against Emperor Yongji and assassinated him to gain command, and his citizens were starved out for four long years. As the food supply within the city walls depleted, grass, bark, rodents, and eventually fellow citizens took the place of more standard nourishment. The once great empire in this sorry state had no choice but to surrender to the lofty terms of Genghis Kahn.
Lessons for a Technology-Enabled Business
Although the defeat of a technology-based based business does not (typically) end in evisceration and decapitation as the history presented above, it does hold the capability to devastate the lives of both the founders and the employees.
Let us identify some of the parallels between the Jin Dynasty, or any empire for that matter, and a tech company (they are the same task ultimately):
- Certain tasks that may jeopardize the entities exist
- There is always a competitor looking to usurp your position
- The role of the leader is to always defend against both external and internal threats while simultaneously growing the entity to provide for the citizens/employees
- A contingency plan is mandatory
As Emperor Yongji failed to acknowledge how central defending the Great Wall was in his role to protect the empire, most technology-based startups we have encountered have failed to realize how central the actual technology in their business plan is to their success. Over half of the companies that approach us have started their journey by looking for a deal, typically from the cheapest software provider possible. Although the software does get completed by these cheap third party entities, often outside the agreed upon deadline and for a much larger budget than proposed, it is more times than not riddled with bugs, clunkiness, and worst of all, written in such a way to incur maximal future technical debt.
Technical debt refers to the notion in software engineering that non-modular, non-commented, and poorly designed source code will incur a very real monetary cost to the business at some point in the future when it is looking to fix, modify, or evolve the software. In contrast to Genghis Khan’s meticulous preparations for a future battle, the business leaders who elect to rely on cheaply created source code, the heart of their business, are setting themselves up for a major hurdle.
It should go without saying: if you are a tech company, meaning your revenue relies on some underlying technical system, extreme effort should be placed into ensuring you are getting the best technology to suit your purposes. Even if you are a non-technical founder or decision maker, it would still be wise to familiarize yourself with the overall topics related to your requirements. You should know the benefits of modular code, how your source code will be stored and transferred to a repository and which one, what language / platform is best for your needs and why, how the software ownership will be structured, and so forth. This does not mean that a more expert consultation cannot deliver a better approach; however, it provides you with a solid footing on which to perform your due diligence in vetting a technical team.

As Genghis Khan was looking to usurp the Jin Empire and seek vengeance for their slaughter of his ancestor Ambaghai Khan, every startup under the sun is facing similar external threat. Just as how the mercenary messenger defected to the Mongolian side and gave up key Jin intelligence, the same concept is enacted every day by third party tech teams who will build the critical infrastructure for another business and then go on to form similar companies or get paid to implement it for the competitors. The de facto response to this is to sign a Non-Disclosure Agreement; however, in reality, these are almost never enforceable in court. It is next to impossible to prove that an entity did not come across proprietary information from another source or think of it on its own prior to the agreement. Either way, once the information has leaked, if it is of any value, this means that a previously established stronghold is soon to be eroded. Further, the trend in the industry is to provide Software as a Service, SaaS, meaning that the client who had purchased the creation of the software does not actually own it or even have access to the source code; rather, they have a license to use it. This often impedes future growth and plans as the company has now ceded great power to a third party.
Touching upon the final two points of leaders needing to always defend and grow their venture, the most compelling argument of cost will be brought up. Anyone who has purchased the creation of software or looked into getting software created knows that it is not a cheap process, especially if you are looking at getting a quality return. Now let us take on the role of a tech-based company that previously had software created by a third party. Keep in mind that the third party was most likely trying to cut all corners to drive up their effective hourly rates by building software laden with technical debt. Once an issue arises from this platform, the company contacts the third party team and pays them another large sum of money, the magnitude of which is directly proporational to the original technical debt the team embedded in the prior deliverable. Then, let us say the company has a novel idea for disrupting their market space and wants to build this into their software. They will once again contact a third party team and pay a large sum of cash which corresponds to the incurred compounding technical debt and the new requirements in order to achieve their vision. Thus, the company’s upper management team is doing little to defend against an outward flow of capital, the possible leaking of secret and proprietary data, and technical malfunctions, and they are stifled in growing their business at a healthy rate by the obstacles they have brought upon themselves.
Proper Approach to Developing Technology
The solution to the quandaries mentioned above is actually quite simple and has been used in growing successful entities throughout history: utilize an internal development team that has stake within the success of your company.

By financing your project with a combination of both equity and capital, you have essentially purchased an internal tech team. Because the equity lowers the amount of upfront capital you would be paying otherwise, further immediate financial risk is mitigated. Also, because operating capital will be higher, this allows the business to grow quicker and tackle new challenges more effectively.
In this case, however, there may be greater upfront temporal investment in order to sell your company to the tech team at the highest valuation. This requires meticulous attention to detail in your business plan and forecasts. This extra step, which is actually often the first step most successful founders undertake, is often neglected; yet, it is critical from even an operations viewpoint for a healthy business.
Overall, there are few, if any, downsides to this strategy while the benefits are vast.
Lesson to Tech Investors
Veteran tech investors know to look at how management is utilizing their human resources. However, we have encountered several novice investors that have previously gambled away and bet on third parties to deliver.
Literally, every competent investor we have met focuses on the stake that critical company figures have and how much sweat equity they are willing to deliver. A third party tech team will provide little or no sweat equity, which not only hinders your technical and business development, but your financing options when and if capital needs to be raised for growth. No serious investor will consider financing your company when they may as well just purchase the third party tech team themselves to deliver the same product or service.




